WordPress updates are critical security and performance improvements that require systematic testing to prevent site breakage. A proper update strategy balances security needs with stability, using staging environments and rollback plans to minimize downtime risks.
What Are WordPress Update Types?
WordPress updates fall into three categories: core updates (WordPress software itself), plugin updates (third-party functionality), and theme updates (design and layout changes). Each type carries different risk levels and requires specific testing approaches.
Core updates subdivide into major releases (adding new features), minor releases (bug fixes and small improvements), and security releases (addressing vulnerabilities). According to WordPress.org statistics, security updates are released every 6-8 weeks on average, while major releases follow a yearly cycle (2023).
Plugin updates vary widely in scope and risk. Simple bug fixes pose minimal risk, while updates adding new features or changing APIs can break existing functionality. WP Engine research shows that plugin conflicts account for 78% of update-related site failures (2023).
Theme updates typically affect visual presentation but can break custom code or child theme modifications. Modern themes using WordPress coding standards experience fewer update issues than legacy themes with custom implementations.
How to Create a Pre-Update Checklist
A systematic pre-update checklist prevents most update-related disasters. Start by documenting your current environment: WordPress version, active plugins with versions, theme details, and custom code modifications.
Create a comprehensive backup before any updates. This includes database exports, complete file system backups, and configuration files. According to Sucuri's annual security report, sites with recent backups recover 85% faster from update failures (2023).
Check plugin and theme compatibility against the target WordPress version. Visit developer websites, review changelogs, and search support forums for known issues. The WordPress Plugin Directory shows compatibility information, but third-party plugins require manual research.
Test critical site functionality manually: user registration, contact forms, e-commerce transactions, and key page loads. Document expected behavior to compare against post-update results.
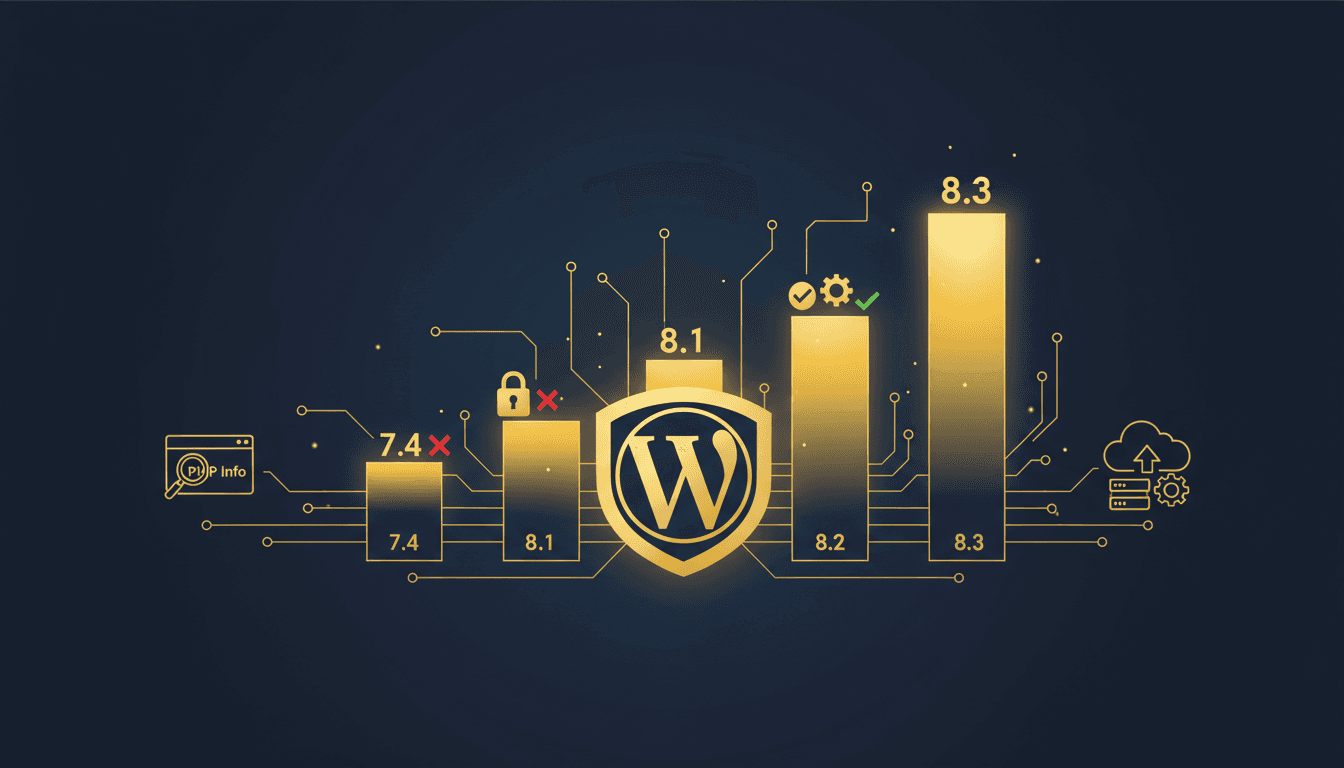
Review server requirements for the target WordPress version. PHP version compatibility, memory limits, and extension requirements can change between releases. Hosting providers like TopSyde automatically handle server compatibility, but self-managed sites need manual verification.
WordPress Staging Environment Testing Workflow
Staging environments are isolated copies of production sites where updates can be tested safely. Create staging sites that mirror production as closely as possible: same server configuration, PHP version, database content, and plugin set.
The staging workflow follows a specific sequence: clone production to staging, apply updates to staging, test functionality thoroughly, then deploy to production only after confirming stability.
Clone your production site including database content, uploaded files, and configuration settings. Many managed hosting providers offer one-click staging creation. For manual setups, use plugins like WP Staging or command-line tools for exact replicas.
Apply updates systematically: WordPress core first, then plugins in order of importance, finally themes. This sequence helps isolate issues to specific components. Test thoroughly after each update before proceeding to the next.
Document test results and any issues discovered. Failed tests require investigation: is the issue critical enough to delay updates, or can it be resolved through configuration changes or plugin replacements?
| Update Component | Testing Priority | Rollback Complexity | Typical Issues |
|---|---|---|---|
| WordPress Core | High | Medium | Theme compatibility, plugin conflicts |
| Security Plugins | Critical | Low | False positive blocks, admin access |
| E-commerce Plugins | Critical | High | Payment processing, order management |
| Performance Plugins | Medium | Low | Caching conflicts, speed regressions |
| Theme Updates | Medium | Medium | Layout breaks, custom code conflicts |
Auto-Update Configuration and Best Practices
WordPress auto-updates handle security patches automatically but require careful configuration for broader update types. Security updates should always auto-install due to their critical nature and minimal risk profile.
Configure auto-updates selectively based on site criticality and risk tolerance. High-traffic commercial sites benefit from manual control over major updates, while low-risk sites can enable broader auto-update scopes.
Core auto-updates can be configured for different release types:
- Security updates: enabled by default, should remain active
- Minor updates: safe for most sites, include bug fixes
- Major updates: disabled by default, require testing
Plugin auto-updates work well for trusted developers with good testing practices. Enable auto-updates for security-focused plugins (Wordfence, Sucuri) and disable for plugins with frequent breaking changes.
Monitor auto-update results through email notifications and dashboard logs. WordPress sends admin emails for successful auto-updates, but failed updates require manual intervention.
Override auto-updates when necessary using constants in wp-config.php:
// Disable all auto-updates
define('AUTOMATIC_UPDATER_DISABLED', true);
// Enable only core security updates
define('WP_AUTO_UPDATE_CORE', 'minor');
// Control plugin auto-updates
add_filter('auto_update_plugin', '__return_false');
How to Handle Update Conflicts and Compatibility Issues
Update conflicts manifest as broken functionality, error messages, or complete site crashes. Systematic troubleshooting identifies problematic components and provides resolution paths.
Plugin conflicts are the most common issue. Deactivate all plugins after an update failure, then reactivate individually to isolate the problematic plugin. Check for plugin updates that address compatibility issues or contact plugin developers for support timelines.
Theme conflicts affect site presentation and functionality. Switch to a default WordPress theme (Twenty Twenty-Four) to test if issues persist. If problems resolve, the active theme has compatibility issues requiring updates or code modifications.
PHP compatibility errors occur when plugins or themes use deprecated functions. Update to compatible versions or replace problematic components. WordPress.org's Plugin Directory shows PHP compatibility ratings for easier decision-making.
Memory limit errors indicate resource consumption increases after updates. Monitor memory usage and increase limits if necessary. Managed hosts like TopSyde automatically handle resource scaling during updates.
Database errors require immediate attention and potential rollbacks. Common causes include plugin database schema changes or corrupted update processes. Always test database-intensive plugin updates in staging first.
Rollback Strategies and Recovery Procedures
Rollback capabilities are essential safety nets when updates cause critical issues. Effective rollback strategies include automated backups, version control systems, and documented recovery procedures.
Database rollbacks are the most critical component. Create database snapshots before updates and test restoration procedures. Full database rollbacks affect all content changes since the backup, so communicate timing carefully to content creators.
File system rollbacks restore plugin and theme files to previous versions. Git-based workflows enable granular rollbacks of specific components. Many managed hosting providers offer one-click rollback functionality for complete site restoration.
Staged rollback procedures minimize downtime:
- Identify the problematic update component
- Attempt fixes without full rollback (plugin deactivation, configuration changes)
- Partial rollback of specific components if fixes fail
- Full site rollback as last resort
Document rollback triggers and procedures. Define specific criteria for rollback decisions: site downtime duration, functionality loss severity, and user impact levels. Clear procedures enable faster decisions during incident response.
Test rollback procedures regularly. Practice database restoration, file rollbacks, and DNS switching in development environments. According to Veeam's data protection report, organizations with tested recovery procedures recover 3x faster from failures (2023).
Update Scheduling for Different Site Types
Update scheduling balances security needs with business requirements. Different site types require different update cadences based on risk tolerance, traffic patterns, and maintenance windows.
High-traffic e-commerce sites need conservative update schedules during low-traffic periods. Schedule major updates during maintenance windows, typically early morning hours with advance customer notification. Security updates require faster deployment despite traffic considerations.
Agency-managed sites benefit from coordinated update schedules across client portfolios. TopSyde's agency hosting solutions enable bulk update management with individual client staging environments for efficient testing workflows.
Development and staging sites should receive updates immediately to maintain parity with production environments. This practice ensures accurate testing environments and early issue detection.
Personal blogs and low-traffic sites can adopt more aggressive update schedules, including broader auto-update configurations. The reduced risk justifies faster deployment of improvements and security fixes.
Create update calendars that coordinate with business cycles, marketing campaigns, and peak traffic periods. Avoid updates during Black Friday, product launches, or other critical business periods.
Managing WordPress Updates at Scale
Large WordPress installations require systematic approaches to update management. Agency portfolios, multisite networks, and enterprise deployments benefit from centralized update tools and standardized procedures.
WordPress multisite networks enable centralized core updates but require individual site testing for plugin and theme updates. Network-activated plugins update across all sites simultaneously, requiring extensive compatibility testing. For detailed multisite management strategies, see our WordPress Multisite Guide.
Third-party management tools like MainWP, ManageWP, and InfiniteWP provide centralized dashboards for multiple WordPress sites. These tools enable bulk updates, centralized staging, and coordinated rollback capabilities across site portfolios.
Managed hosting providers specializing in WordPress offer enterprise-grade update management. Features include automated staging, compatibility testing, and coordinated update deployment across multiple sites with rollback capabilities.
Implement update policies for team-managed sites:
- Define approval workflows for different update types
- Establish testing requirements and sign-off procedures
- Create communication protocols for update schedules and results
- Document rollback authority and decision-making processes
Monitor update success rates and failure patterns across your portfolio. Identify plugins or themes with frequent update issues and consider replacements. Track update-related support tickets to optimize testing procedures.
WordPress Update Automation Tools and Scripts
Automation reduces manual effort while maintaining safety standards. WP-CLI enables scriptable WordPress updates with granular control over update types and error handling.
Basic WP-CLI update commands:
# Check for available updates
wp core check-update
wp plugin list --update=available
wp theme list --update=available
# Update WordPress core
wp core update
# Update all plugins
wp plugin update --all
# Update specific plugins
wp plugin update akismet wordfence
Combine WP-CLI with backup scripts for safer automation:
#!/bin/bash
# Backup before updates
wp db export backup-$(date +%Y%m%d-%H%M%S).sql
tar -czf files-backup-$(date +%Y%m%d-%H%M%S).tar.gz wp-content/
# Perform updates
wp core update
wp plugin update --all
# Verify site functionality
wp eval 'wp_remote_get(home_url());'
GitHub Actions and similar CI/CD tools can automate update testing in staging environments. Create workflows that clone production, apply updates, run automated tests, and notify administrators of results.
Monitoring tools should track update success rates, performance impacts, and error rates. Set up alerts for failed updates, security vulnerabilities, and performance regressions following updates.
Update Security Considerations
Security-focused update strategies prioritize vulnerability patches while maintaining site stability. Security updates often require immediate deployment, even outside regular maintenance windows.
Monitor WordPress security announcements through official channels: WordPress.org news, security mailing lists, and vulnerability databases. Security updates typically receive same-day deployment recommendations regardless of other scheduling considerations.
Plugin vulnerability monitoring requires third-party tools since WordPress doesn't centrally track plugin security issues. Services like WPScan, Wordfence Intelligence, and Patchstack provide vulnerability alerts for WordPress plugins and themes.
Implement security update exception processes that bypass normal testing workflows for critical vulnerabilities. These fast-track procedures should include:
- Immediate staging deployment and basic functionality testing
- Production deployment within hours of testing completion
- Enhanced monitoring for security-related issues
- Rollback procedures optimized for speed over thorough testing
Balance security urgency with stability needs. Critical security updates warrant accepting higher risk of minor functionality issues, while less severe vulnerabilities can follow normal testing workflows.
For comprehensive WordPress security strategies beyond updates, reference our WordPress Security Best Practices guide.
Frequently Asked Questions
How often should I update WordPress core, plugins, and themes?
WordPress core security updates should be applied immediately, ideally within 24-48 hours of release. Minor core updates can follow weekly or bi-weekly schedules, while major updates require thorough testing and can be scheduled monthly. Plugin and theme updates depend on the specific component's stability and your site's risk tolerance, but security-related updates should be prioritized regardless of scheduled maintenance windows.
Should I enable automatic updates for WordPress?
Enable automatic updates for WordPress core security patches and minor releases, as these have minimal risk and critical security benefits. Plugin auto-updates work well for trusted security plugins (Wordfence, Sucuri) and simple utility plugins, but disable auto-updates for complex plugins like page builders, e-commerce solutions, or plugins that frequently release breaking changes. Always maintain manual control over major WordPress core updates.
What's the safest way to update WordPress without breaking my site?
Create a full backup first, then test all updates in a staging environment that mirrors your production site exactly. Update WordPress core first, followed by plugins in order of importance, then themes. Test critical functionality after each component update, and document any issues before proceeding. Only deploy to production after confirming everything works correctly in staging, and keep rollback procedures ready in case issues appear post-deployment.
How do I handle plugin conflicts after a WordPress update?
Deactivate all plugins immediately after identifying conflicts, then reactivate them one by one to isolate the problematic plugin. Check for updated versions of conflicting plugins that address compatibility issues, or contact plugin developers for support timelines. If no fix is available, consider alternative plugins that provide similar functionality, or temporarily disable the conflicting plugin until compatibility is restored.
What should I do if a WordPress update breaks my site?
First, don't panic – implement your rollback plan immediately. Restore from your pre-update backup if you have one, or use your hosting provider's rollback features. If partial rollback is possible, deactivate recently updated plugins or switch to a default theme to isolate the issue. Document what broke and when, then investigate solutions in your staging environment before attempting fixes on production.

Senior WordPress Engineer
8+ years WordPress & WooCommerce development
Rachel is a senior WordPress engineer at TopSyde specializing in WooCommerce performance and plugin architecture. She has built and maintained high-traffic e-commerce sites processing millions in annual revenue.