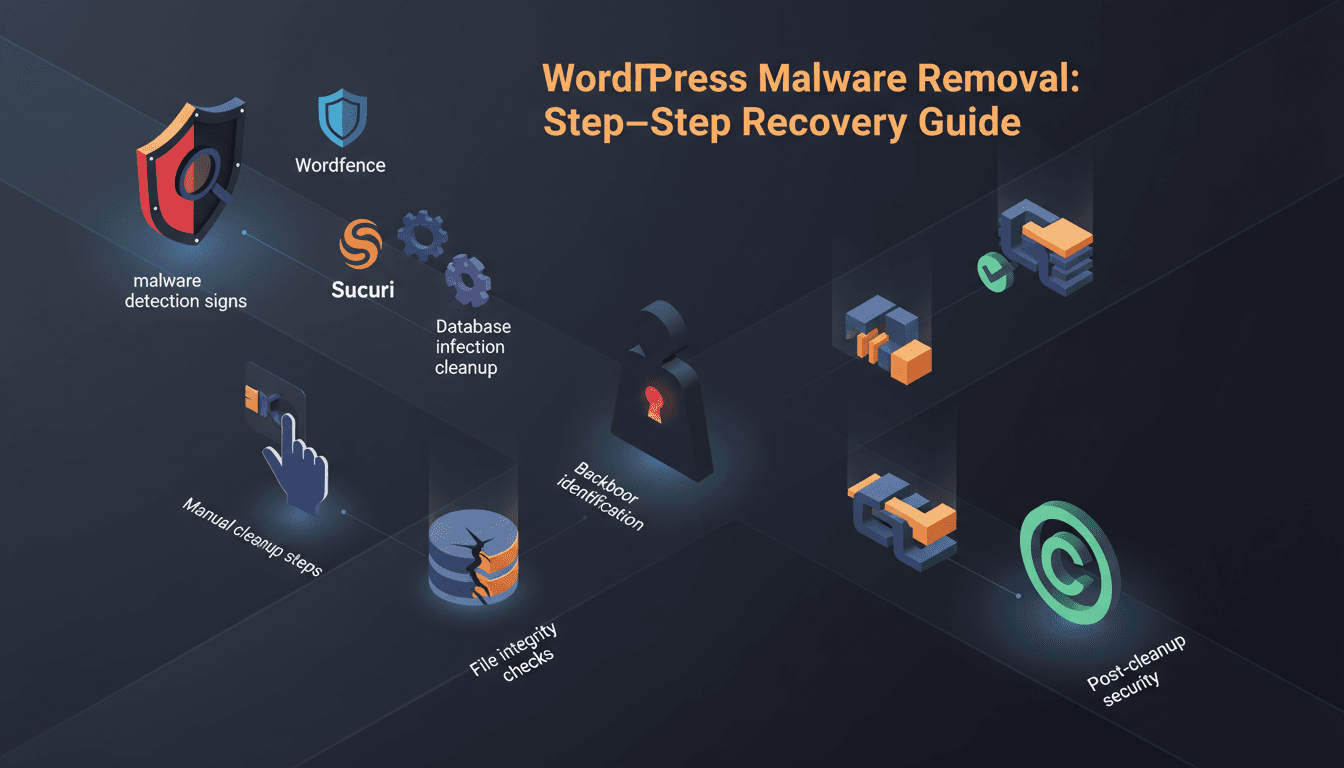
WordPress malware removal requires systematic detection, isolation, and cleanup of malicious code from files, databases, and server configurations. Success depends on identifying infection vectors, removing all traces, and implementing prevention measures to prevent reinfection.
What Are the Early Signs of WordPress Malware?
WordPress malware manifests through performance degradation, unauthorized redirects, and suspicious administrative changes before users typically notice visual symptoms. According to Sucuri's Website Security Report, 94% of infected WordPress sites show detectable signs within 24-48 hours of initial compromise (2024).
Performance and Accessibility Issues
Malware commonly causes:
- Slow page load times due to cryptocurrency mining scripts or botnet participation
- Random redirects to pharmaceutical, gambling, or adult content sites
- Search engine warnings displaying "This site may be compromised" messages
- Hosting provider suspensions for excessive resource usage or spam distribution
Administrative and Content Changes
Monitor your WordPress admin for:
- Unauthorized user accounts with administrator privileges
- Unknown plugins or themes installed without your knowledge
- Modified core files with unusual timestamps or file sizes
- Spam content injection in posts, pages, or comments
Server-Level Indicators
Check server logs for:
# Excessive 404 errors from scanning attempts
grep "404" /var/log/apache2/access.log | tail -20
# Suspicious file access patterns
grep -i "eval\|base64\|gzinflate" /var/log/apache2/access.log
How to Scan WordPress for Malware
Comprehensive malware detection combines automated security plugins, online scanners, and manual file system analysis. Each method reveals different infection types and attack vectors.
Security Plugin Scanning
Wordfence Security provides real-time scanning with premium features:
// Enable Wordfence API scanning
define('WFWAF_SUBDIRECTORY_INSTALL', 1);
define('WFWAF_AUTO_PREPEND', 1);
Install and configure:
- Install Wordfence from WordPress admin
- Run initial scan: Wordfence > Scan
- Review critical issues first, then high-priority items
- Compare files against WordPress.org repository checksums
Sucuri Security offers complementary scanning:
- Monitors DNS changes and blacklist status
- Detects server-side malware missed by other tools
- Provides detailed infection timeline analysis
Online Security Scanners
Sucuri SiteCheck (free external scanner):
- Analyzes public-facing content for malware
- Checks blacklist status across major providers
- Identifies malicious redirects and iframes
VirusTotal integration:
# Submit suspicious files for multi-engine analysis
curl --request POST \
--url https://www.virustotal.com/vtapi/v2/file/scan \
--form apikey=YOUR_API_KEY \
--form file=@suspicious-file.php
Manual File System Analysis
Search for common malware patterns:
# Find recently modified PHP files
find /path/to/wordpress -name "*.php" -mtime -7 -ls
# Search for encoded malware signatures
grep -r "eval(base64_decode" /path/to/wordpress/
grep -r "gzinflate(base64_decode" /path/to/wordpress/
grep -r "assert(base64_decode" /path/to/wordpress/
# Identify suspicious file permissions
find /path/to/wordpress -type f -perm 777
Step-by-Step Manual Malware Cleanup
Manual cleanup ensures complete malware removal when automated tools miss sophisticated infections or when dealing with custom malware variants.
1. Create Complete Site Backup
Before cleanup, secure a complete backup:
# Database backup
mysqldump -u username -p database_name > backup_$(date +%Y%m%d).sql
# File system backup
tar -czf site_backup_$(date +%Y%m%d).tar.gz /path/to/wordpress/
For comprehensive backup strategies, see our WordPress Backup Strategy guide.
2. Isolate and Analyze Infected Files
Quarantine suspicious files:
# Move infected files to quarantine directory
mkdir /tmp/malware_quarantine
mv /path/to/infected-file.php /tmp/malware_quarantine/
Decode obfuscated malware:
<?php
// Safe decoding script (run in isolated environment)
$encoded = "base64_encoded_string_here";
echo base64_decode($encoded);
?>
3. Clean WordPress Core Files
Restore core file integrity:
# Download fresh WordPress core
wget https://wordpress.org/latest.tar.gz
tar -xzf latest.tar.gz
# Replace core files (preserve wp-config.php and .htaccess)
rsync -av wordpress/ /path/to/your/site/ --exclude=wp-config.php --exclude=.htaccess
4. Sanitize wp-config.php
Review and clean wp-config.php:
<?php
// Remove any suspicious code additions
// Verify database credentials
define('DB_NAME', 'database_name');
define('DB_USER', 'username');
define('DB_PASSWORD', 'password');
define('DB_HOST', 'localhost');
// Update security keys
define('AUTH_KEY', 'new-unique-key-here');
define('SECURE_AUTH_KEY', 'new-unique-key-here');
// ... generate all 8 keys from https://api.wordpress.org/secret-key/1.1/salt/
?>
How to Clean Malware from WordPress Database
Database infections often persist after file cleanup, requiring targeted SQL queries to identify and remove malicious content from core WordPress tables.
Scan wp_posts Table
Malware frequently injects spam content:
-- Find posts with suspicious content
SELECT ID, post_title, post_content
FROM wp_posts
WHERE post_content LIKE '%<script%'
OR post_content LIKE '%iframe%'
OR post_content LIKE '%eval(%'
OR post_content LIKE '%base64%';
-- Clean specific malware patterns
UPDATE wp_posts
SET post_content = REPLACE(post_content, 'malicious_code_here', '')
WHERE post_content LIKE '%malicious_code_here%';
Clean wp_options Table
Check for infected options:
-- Identify suspicious options
SELECT option_name, option_value
FROM wp_options
WHERE option_value LIKE '%<script%'
OR option_value LIKE '%eval(%'
OR option_value LIKE '%base64%'
OR option_name LIKE '%_transient_%';
-- Remove malicious transients
DELETE FROM wp_options
WHERE option_name LIKE '%_transient_timeout_%'
OR option_name LIKE '%_transient_%';
Audit User Accounts
Remove unauthorized administrators:
-- List all administrator users
SELECT ID, user_login, user_email, user_registered
FROM wp_users u
JOIN wp_usermeta um ON u.ID = um.user_id
WHERE um.meta_key = 'wp_capabilities'
AND um.meta_value LIKE '%administrator%';
-- Remove suspicious admin accounts
DELETE FROM wp_users WHERE ID = suspicious_user_id;
DELETE FROM wp_usermeta WHERE user_id = suspicious_user_id;
How to Identify and Remove WordPress Backdoors
Backdoors provide persistent access for attackers and often survive initial cleanup attempts. According to Wordfence's Threat Intelligence Report, 47% of infected sites contain multiple backdoor files (2024).
Common Backdoor Locations
Search high-risk directories:
# WordPress core directories (should contain no custom files)
find wp-admin/ wp-includes/ -name "*.php" -type f | xargs grep -l "eval\|system\|exec\|passthru"
# Plugin and theme directories
find wp-content/ -name "*.php" -type f -mtime -30 | xargs grep -l "base64_decode\|gzinflate"
# Check for hidden files
find . -name ".*" -type f | grep -v ".htaccess\|.git"
Backdoor Pattern Detection
Common backdoor signatures:
# Web shells and command execution
grep -r "system(\$_" wp-content/
grep -r "\$_POST\[" wp-content/ | grep -i "eval\|system\|exec"
# File upload backdoors
grep -r "move_uploaded_file" wp-content/ | grep -v "wp-includes"
# Database connection backdoors
grep -r "mysql_connect\|mysqli_connect" wp-content/ | grep -v "wp-config"
Backdoor Removal Process
| Backdoor Type | Location | Removal Method |
|---|---|---|
| Web Shell | wp-content/uploads/ | Delete files, check upload restrictions |
| Plugin Backdoor | wp-content/plugins/ | Remove plugin, scan similar plugins |
| Theme Backdoor | wp-content/themes/ | Replace theme files, check functions.php |
| Core Injection | wp-admin/, wp-includes/ | Restore from clean WordPress download |
WordPress File Integrity Verification
File integrity checks confirm complete malware removal and identify any remaining compromised files through checksum comparison and core file validation.
WordPress Core Integrity
Verify core files against official checksums:
# Download WordPress checksums
wget https://api.wordpress.org/core/checksums/1.0/?version=6.4.2
# Compare local files (custom script)
#!/bin/bash
for file in $(find wp-admin wp-includes -name "*.php"); do
local_hash=$(sha1sum "$file" | cut -d' ' -f1)
# Compare against official checksums
echo "$file: $local_hash"
done
Plugin and Theme Verification
Check for modifications:
<?php
// Plugin integrity checker
function check_plugin_integrity($plugin_slug) {
$plugin_data = get_plugin_data(WP_PLUGIN_DIR . '/' . $plugin_slug);
$version = $plugin_data['Version'];
// Compare against WordPress.org version
$api_url = "https://api.wordpress.org/plugins/info/1.0/$plugin_slug.json";
$response = wp_remote_get($api_url);
if (!is_wp_error($response)) {
$body = wp_remote_retrieve_body($response);
$plugin_info = json_decode($body, true);
if ($plugin_info['version'] !== $version) {
error_log("Plugin $plugin_slug version mismatch");
}
}
}
?>
File Permission Audit
Secure file permissions:
# WordPress recommended permissions
find /path/to/wordpress/ -type d -exec chmod 755 {} \;
find /path/to/wordpress/ -type f -exec chmod 644 {} \;
chmod 600 wp-config.php
Post-Cleanup Security Hardening
Hardening prevents reinfection by addressing vulnerabilities that enabled initial compromise and implementing monitoring systems for early threat detection.
Update All Components
Systematic updates:
# WordPress core update via WP-CLI
wp core update
wp core verify-checksums
# Plugin updates
wp plugin list --update=available
wp plugin update --all
# Theme updates
wp theme list --update=available
wp theme update --all
Security Configuration
Implement security headers in .htaccess:
# Security headers
Header always set X-Content-Type-Options nosniff
Header always set X-Frame-Options DENY
Header always set X-XSS-Protection "1; mode=block"
Header always set Strict-Transport-Security "max-age=63072000; includeSubDomains; preload"
# Disable file execution in uploads
<Directory "/path/to/wp-content/uploads/">
<Files "*.php">
Order Deny,Allow
Deny from All
</Files>
</Directory>
Monitoring and Alerting
Configure ongoing monitoring:
<?php
// File change monitoring
function monitor_core_files() {
$core_files = ['wp-config.php', '.htaccess', 'index.php'];
foreach ($core_files as $file) {
if (file_exists($file)) {
$current_hash = sha1_file($file);
$stored_hash = get_option("file_hash_$file");
if ($stored_hash && $current_hash !== $stored_hash) {
// Alert administrators
wp_mail(get_option('admin_email'),
'File Change Alert',
"Core file $file has been modified");
}
update_option("file_hash_$file", $current_hash);
}
}
}
add_action('wp_loaded', 'monitor_core_files');
?>
For comprehensive security measures, review our WordPress Security Best Practices guide.
WordPress Malware Prevention Strategies
Prevention requires proactive security measures, regular maintenance, and hosting environment hardening to minimize attack surfaces and detect threats early.
Automated Security Monitoring
Implement continuous monitoring:
- Real-time file system monitoring for unauthorized changes
- Failed login attempt tracking with IP-based blocking
- Plugin/theme vulnerability scanning against known CVE databases
- Malware signature updates for emerging threat detection
Managed Security Solutions
TopSyde's managed hosting includes comprehensive security features:
- Automated malware scanning and removal
- Real-time threat detection with AI-powered analysis
- Proactive security patches and updates
- 24/7 security monitoring with incident response
- DDoS protection and firewall management
Starting at $89/month, managed security eliminates manual security management overhead.
Backup and Recovery Planning
Maintain robust backup systems:
# Automated daily backups
#!/bin/bash
DATE=$(date +%Y%m%d_%H%M%S)
mysqldump -u $DB_USER -p$DB_PASS $DB_NAME > backup_$DATE.sql
tar -czf files_$DATE.tar.gz /path/to/wordpress/
For detailed backup strategies, see our WordPress Backup Strategy guide.
Keep Reading on TopSyde
- WordPress Accessibility: Complete WCAG 2.2 Compliance Guide — Master WordPress accessibility with our WCAG 2.2 compliance guide. Learn accessible themes, plugin audits, screen reader testing, and legal requirements.
- WordPress API Rate Limiting & DDoS Protection Guide — Complete guide to WordPress API rate limiting, DDoS protection, and security hardening. Includes REST API limits, WAF setup, and bot detection strategies.
- Full technical spec sheet
- Our infrastructure stack
Frequently Asked Questions
How long does WordPress malware removal typically take?
Complete malware removal typically takes 2-6 hours depending on infection severity and site complexity. Simple spam injections resolve within 1-2 hours, while sophisticated backdoor networks or database compromises require 4-6 hours for thorough cleanup and verification.
Can I remove WordPress malware without technical expertise?
Basic malware removal is possible using security plugins like Wordfence or Sucuri, but complex infections often require manual file analysis and database cleanup. Consider managed hosting solutions or security professionals for comprehensive removal and prevention.
Will malware removal affect my site's SEO rankings?
Proper malware removal typically improves SEO by eliminating spam content and blacklist penalties. However, avoid mass content deletions or URL structure changes during cleanup. Search engines generally restore rankings within 2-4 weeks after successful malware removal and security improvements.
How can I prevent WordPress malware reinfection?
Prevent reinfection through regular updates,
Topics

DevOps & Security Lead
12+ years DevOps, Linux & cloud infrastructure certified
Marcus leads infrastructure and security at TopSyde, managing the server fleet and AI monitoring systems that keep client sites fast and protected. Former sysadmin turned WordPress hosting specialist.